Data Integrity for International Cold Chain IoT: Buffering, Resends, Idempotency, and Audit Trails
This article complements the GPT29 Cold Chain White Paper.
Download the PDF: GPT29 Cold Chain Tracking for Freezers — Engineering & Compliance White Paper
Why data integrity is the foundation of compliance and claims
Many cold chain programs focus on sensors first: temperature, humidity, light, shock. But in investigations, the most painful failure mode is not a missing sensor—it is a broken timeline. If there are gaps, duplicates, or inconsistent timestamps, stakeholders can’t confidently answer: “What happened, where, and for how long?”
A defensible record requires that telemetry remains coherent across:
- coverage gaps (offline windows),
- resends (duplicate risk),
- handoffs (time and location context), and
- policy changes (rule versions).
-

The ultimate goal: A complete, tamper-evident audit trail with recovered data gaps and synchronized UTC timestamps for compliance
Common causes of integrity failure on overseas routes
- Metal shielding in freezers and reefer containers reduces signal strength and increases retries.
- Port/terminal infrastructure creates intermittent connectivity, especially during yard staging.
- Roaming behavior may change network performance by country and carrier.
- Time drift can occur if device clocks are not managed consistently.
- Backend retries and at-least-once delivery pipelines can introduce duplicates if not deduplicated properly.
Installation and placement affect connectivity; see: Installing Trackers on Freezers and Reefer Containers (Practical Guide).
Core pattern: Store-and-forward (buffer locally, forward when online)
A widely used approach for international IoT telemetry is store-and-forward:
- When connectivity is available, transmit telemetry at your configured interval.
- When offline, buffer records on-device (telemetry points and event summaries).
- When connectivity returns, replay buffered records in order, using a dedupe-safe key.
This protects the evidence timeline even when real-time visibility is impossible at certain legs.
Engineering note: buffer what investigators need
Buffering does not mean transmitting “everything.” For long missions, it can be more efficient to:
- buffer periodic telemetry, and
- buffer event summaries (excursions, exposure, shocks) so investigators have structured incidents even if raw telemetry is sparse.
Resend logic: protect battery while preserving continuity
Resends are necessary, but uncontrolled retries can drain battery quickly—especially inside metal enclosures. A practical resend strategy includes:
- Exponential backoff for retry intervals.
- Retry ceilings to avoid infinite loops in low-coverage zones.
- Priority ordering: send high-value event summaries first (excursions, severe shocks), then baseline telemetry.
- Batching buffered records to reduce protocol overhead.
This is tightly connected to mission planning and 60+ day battery targets: Designing a 60+ Day Battery Mission for Freezer & Reefer Tracking.
Idempotency: the antidote to duplicate records
In real IoT systems, at-least-once delivery is common. The device might resend a packet after a timeout, or your backend might replay messages after a transient failure. Without deduplication, you can end up with duplicate telemetry points—which breaks reports and excursions.
The solution is idempotency: each record carries a unique identifier so the ingestion system can safely accept duplicates without double-counting. Common approaches include:
- Monotonic sequence number per device (recommended if feasible).
- Idempotency key derived from device ID + timestamp + record type + sequence.
- Event IDs for excursions and incidents (so “start” and “end” can be linked).
Example idempotency key (conceptual)
idempotency_key = SHA256(device_id + "|" + record_type + "|" + sample_timestamp_utc + "|" + seq)
Your backend stores idempotency keys (or sequence numbers) and rejects duplicates. This allows safe resends during unstable connectivity.
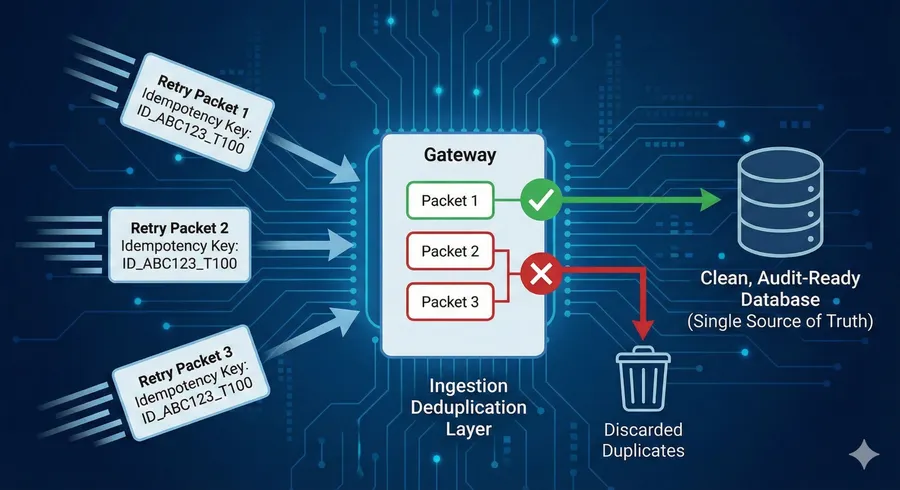
Idempotency at work. The gateway uses unique keys to automatically reject duplicate transmissions, preventing data corruption
Timestamps: pick a consistent time policy (UTC is common)
Global operations cross time zones. If you do not standardize timestamps, investigations become slow and error-prone. A practical approach is:
- device stores and transmits UTC timestamps,
- backend stores UTC and converts for UI/reporting, and
- events record both device timestamp and ingestion timestamp when useful.
For excursion definitions, consistent time semantics are required: Temperature Excursions: Threshold + Duration.
Tamper-evident records: optional but valuable for claims
For programs that require stronger evidence, consider tamper-evident techniques:
- Hash chaining: each record includes a hash of the previous record, creating an integrity chain.
- Digital signatures: device signs record batches; backend verifies signatures.
- Policy versioning: include rule IDs and configuration versions in events.
The goal is not “blockchain.” The goal is simply to strengthen confidence that records were not modified after capture. The appropriate approach depends on your claims environment and system architecture.
Integration guidance: build an ingestion pipeline that stays clean at scale
Once integrity controls are in place, ingestion becomes predictable. Recommended pipeline stages include:
- Transport layer (MQTT/HTTPS, etc.) with authentication and rate controls.
- Deduplication using idempotency keys / sequence numbers.
- Normalization of units and field names (temperature units, timestamps).
- Event generation (excursions, exposure, shocks) if not already done on-device.
- Storage optimized for time-series queries and audits.
- Alerting & reporting in your platform.
See the integration-focused article: Integrating GPT29 Telemetry into Your Platform (API Patterns + Examples).
Download the white paper
The GPT29 cold chain white paper provides a deeper blueprint for continuity controls, event modeling, installation reality, and pilot acceptance criteria.
Download (PDF): GPT29 Cold Chain Tracking for Freezers — Engineering & Compliance White Paper
Questions? Contact EELink or email [email protected].
FAQ
Is buffering always necessary?
For international routes with known coverage gaps, buffering is strongly recommended. Without it, you risk missing the very incident windows that matter most.
Where should deduplication happen?
Ideally at the ingestion boundary (as early as possible), so downstream systems—databases, reports, alerts—see a clean, consistent stream.







